
Why trustee accountability has changed
Picture a membership body that has just discovered a data breach. The systems are back up, but the first questions from regulators are for the trustees:
- What did the board know,
- What did it do, and
- Where is the evidence?
Those questions capture how far trustee accountability in the digital age has moved beyond “did we buy the right software”. For membership bodies, accountability for data protection, cybersecurity and business continuity now sits squarely with the board, even when operational work is delegated to staff, volunteers, or suppliers.
Trustee accountability in the digital age means being able to show that your board has identified digital risks, set expectations, resourced proportionate controls, and regularly checked that those controls work in practice.
What the law expects of trustees
If your membership body handles personal data – and almost all do – you sit under UK GDPR and the Data Protection Act 2018, with the Data (Use & Access) Act 2025–26 (DUAA) updating how some obligations work in practice. In legal terms, the organisation is the data controller, but trustees carry collective responsibility for ensuring that controller duties are discharged, not quietly left to “the system” or “the IT person”.
The ICO’s accountability and governance guidance makes this explicit: organisations must not only comply with UK GDPR, they must be able to demonstrate how they comply. Regulators frame this through the principle of accountability, which runs through the ICO’s Accountability Framework.
For trustees, the practical effect is simple. You do not need to memorise every article of UK GDPR, but you do need to be confident that:
- Someone senior owns data protection and information security day to day.
- The board has seen and approved a clear, proportionate approach to privacy, cybersecurity and business continuity.
- You receive regular, comprehensible reporting on how that approach is working, including near misses and weaknesses.
DUAA increases the stakes for membership organisations in particular. Guidance such as MemberWise’s explainer on how the Data (Use & Access) Act 2025 impacts your membership organisation stresses new expectations around documenting decisions about data access, use and complaints handling. Trustees may not manage those processes, but they will be asked how they oversee them.
Myth and reality around personal liability
Trustees often ask whether they are personally on the hook if something goes wrong. The legal answer is nuanced, but the governance answer is consistent: you cannot outsource your duty of care.
In most cases, enforcement action for data protection failures is taken against the organisation as controller, not individuals. The ICO’s focus is on whether there is accountability in practice, not simply a named role on a chart. Where trustees risk personal exposure is when regulators conclude that they have been reckless, persistently ignored obvious risks, or failed to act on clear warnings about weaknesses in areas like cybersecurity or continuity.
A practical way to think about this is to ask: “If the ICO or Charity Commission read our board minutes for the past two years, would they see that we took digital risk seriously?” Commentary on UK cyber and data risk increasingly underlines this link between governance, accountability and board-level scrutiny. That does not mean every trustee needs to become a cyber expert. It does mean that boards should:
- Challenge overly optimistic assumptions such as “we’ve never had a problem so we must be fine”.
- Insist on seeing risk registers that include data protection, cyber and continuity in specific terms, not just “IT risk”.
- Follow through on agreed actions, particularly where external auditors or advisers have flagged weaknesses.
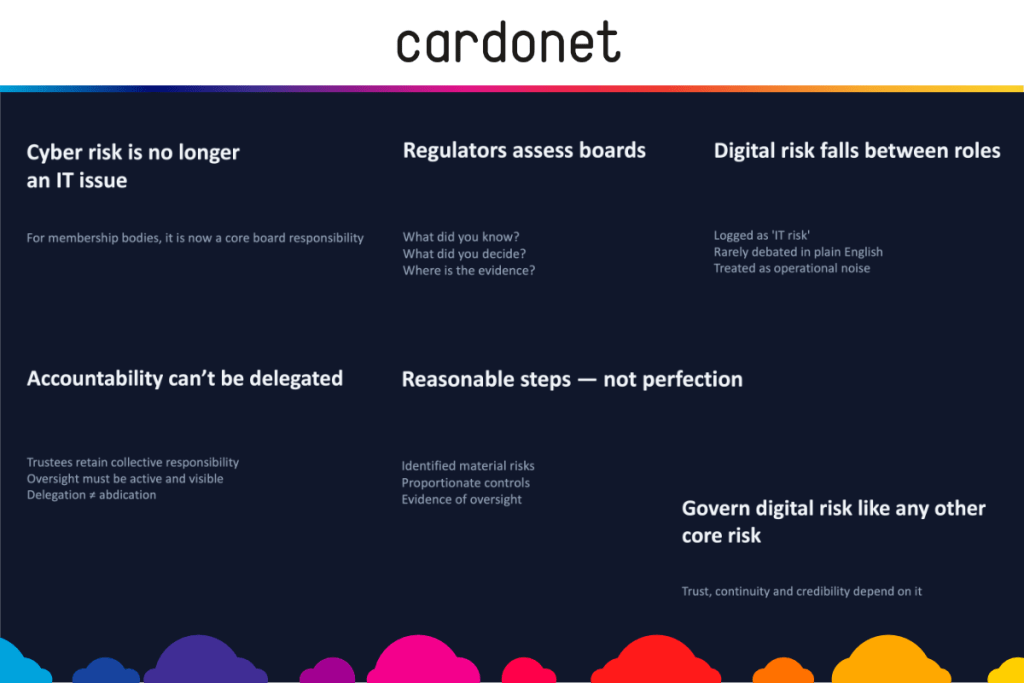
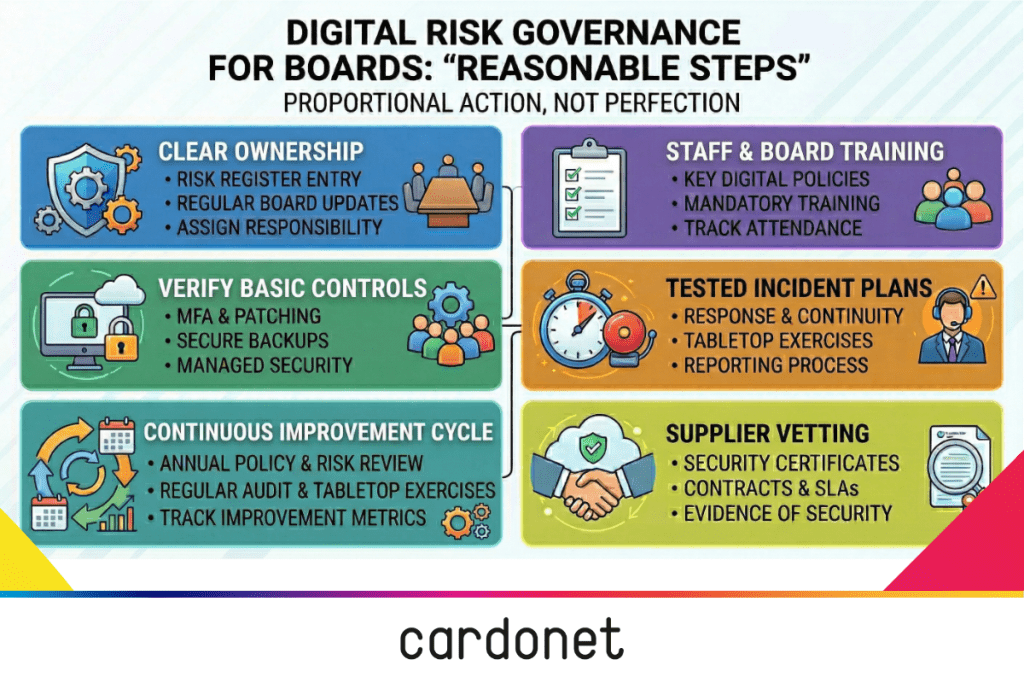
What “reasonable steps” looks like for a membership body board
Regulators rarely demand perfection. They look for reasonable steps, taken proportionately to your size, data sensitivity and resources. For a membership body, those steps tend to fall into five areas.
1. Governance and risk ownership
Trustees should make sure that digital risk has a clear home in the governance structure. That often means explicit responsibility in the terms of reference for an audit and risk or finance and risk committee, with cyber, data protection and continuity appearing by name in the risk register. The full board should see at least an annual deep dive on these topics, framed in member impact, regulatory exposure and reputational terms rather than server diagrams.
You do not need a new committee to achieve this. What you need is clarity around who owns oversight for digital risk, how often it reaches the board, and how the board checks that agreed actions actually happen.
2. Policies, training and culture
Reasonable steps always include policy and training. For a membership body, that usually means up to date, board approved policies covering data protection, information security, acceptable use, remote working and incident response, written in language that staff and volunteers can follow.
Sector guidance such as the 2025 annual data protection checklist stresses that policies and staff awareness are central to demonstrating accountability, not optional extras. Trustees should expect to see induction and refresher training on data protection and cyber awareness for staff, volunteers and (crucially) trustees themselves, with attendance tracked so you can prove it happened. If your volunteers have access to member data, they need proportionate guidance on what they can and cannot do with that data.
3. Technical controls: boards do not configure, they confirm
Trustees are not there to pick encryption algorithms. You are there to ask, “Are the basics in place, and how do we know?” That means seeking assurance that controls such as access management, multi factor authentication, regular patching, secure backups and device encryption are not just on a wish list but implemented and monitored.
For many membership bodies, that assurance will come through a managed IT or cybersecurity partner that provides monitoring, patching and security services, with clear reporting and alerts. Services such as Cardonet’s Managed SOC Service give you continuous threat monitoring, incident detection and response coordination that can be reported to trustees in plain language. The board’s job is to define the outcomes it expects (for example, recovery time if systems fail, data retention standards, audit trails) and then check whether management and suppliers can demonstrate that those outcomes are realistic and being met.
Backups are a good example. Best practice such as the 3-2-1 rule for data backups is well established, but many boards have never asked whether their organisation follows it. A reasonable trustee question is simply: “How do we back up our critical systems and how do we know those backups will work when we need them?”
4. Incident and continuity planning
A board that has never seen an incident response plan or business continuity plan is not taking reasonable steps. Trustees should insist that these documents exist, are tailored to the organisation, and have been tested at least through a tabletop exercise.
Charity law specialists analysing recent updates to Charity Commission serious incident reporting highlight the expectation that boards recognise and report serious cyber and data incidents promptly, based on clear internal criteria.
In practice, that means you should be able to answer questions like:
- Who decides whether something is a notifiable data breach, and who informs the ICO and affected members?
- How quickly can we restore key systems from backups, and when was that last tested?
- How will we communicate with members, staff and partners during a serious outage or cyber incident?
Trustees do not need to write these plans, but they should review the high level, ask whether the scenarios are realistic, and ensure that responsibilities are clear even if key individuals are unavailable. A partner offering a Managed Cyber Incident Response Service can help design, rehearse and operate those plans, giving boards confidence that their paperwork will stand up in a real incident.
5. Supplier oversight and evidence
Most membership bodies rely heavily on third parties for IT, cloud platforms and membership databases. Under UK GDPR and DUAA, you remain responsible for what your processors do with your members’ data, even when those processors are large platforms with their own compliance badges.
Reasonable steps include checking that key suppliers:
- Have appropriate security certifications or controls (for example Cyber Essentials or ISO 27001 for IT and hosting providers).
- Offer contract terms and SLAs that reflect your risk appetite and regulatory duties, including support for incident handling and access to logs where needed.
- Can provide documentation on how they protect data and handle incidents, not just marketing assurances.
Here, partnering with a provider that offers managed cybersecurity services, incident response support and ongoing IT security services can give trustees the evidence trail they need for regulators, insurers and funders. Cardonet’s overview of IT services, IT support, consultancy and cyber security illustrates the kind of integrated support model that can underpin this governance.
A trustee accountability checklist for your next board meeting
You do not need a 40-page report to start raising the bar. You need better questions. At your next board or committee meeting, you could use this checklist:
- Risk and oversight – Where in our risk register do data protection, cybersecurity and business continuity appear, and when did we last review them in depth?
- Policies and training – When were our key digital policies last updated, and what proportion of staff, volunteers and trustees have completed relevant training in the past 12 months?
- Technical assurance – How do we know that critical controls like backups, access management and updates are actually in place and working, rather than just assumed?
- Incident readiness – Do we have an incident response and continuity plan, who has seen it, and when was it last exercised, even on paper?
- Supplier due diligence – Which of our key IT and cloud suppliers hold formal security certifications, and how do we monitor their ongoing performance and compliance?
None of these questions require technical expertise. They do require trustees to be willing to sit with the discomfort of honest answers and to make time for follow through.
Using IT and security partners to support your duties
For many membership bodies, the gap is not awareness but capacity. You may have a single “accidental IT manager”, a part time operations lead, or a small internal team already stretched thin. This is where trusted IT and cybersecurity partners can help boards move from aspiration to evidence.
Partners that offer cybersecurity services such as cyber security audits, managed security services, incident response planning and cloud security services can provide structured assessments, improvement roadmaps and regular reporting that speak directly to trustee responsibilities. A managed IT services provider can take ownership of operational tasks like patching, monitoring, backup and 24/7 support, while giving the board simple dashboards and KPIs to track performance over time, as described in Cardonet’s IT services, IT support, consultancy and cyber security summary.
For trustees, the key is to treat these relationships as an extension of governance, not just procurement. That means asking about security credentials, understanding how incidents are handled, and ensuring that service reports feed into board packs in language nonspecialists can understand.
Why this matters for reputation and resilience
Digital risk is not abstract. For membership bodies, your reputation rests on trust: that members’ data is safe, that services will be available when they need them, and that you will handle problems transparently and fairly. High profile incidents in the charity and membership sector show how quickly confidence can evaporate when systems fail or data is mishandled, and recent commentary on serious incident reporting reinforces that boards are expected to be proactive, not passive, about those risks.
Regulators have also signaled that expectations are rising. DUAA, updated Charity Commission guidance and the ICO’s accountability framework all point in the same direction: boards are expected to show active engagement with digital risk, not rely on assurances that “IT has it covered”. For many bodies, demonstrating that engagement will be as important for funders, insurers and key partners as it is for regulators.
In our experience working with membership organisations, the boards that cope best with digital shocks are rarely the ones with the flashiest systems. They are the ones that know where their risks sit, have rehearsed what they will do when something goes wrong, and can show their members and regulators a clear, honest story about how they govern technology.
Protecting your membership body: next steps
If this feels daunting, start small and practical. Put “trustee accountability for digital risk” as a named item on your next board agenda, and use the checklist above to frame the discussion.
Ask your executive team for a short paper that maps current controls against the “reasonable steps” areas in this article, highlighting gaps and dependencies on specific individuals or suppliers. Then agree two or three concrete actions, such as commissioning a cyber security audit, refreshing policies and training, or running a tabletop incident exercise with your senior team and key trustees.
If you already work with an IT or cybersecurity partner, involve them in this conversation. Use their expertise to translate technical details into governance language and to turn your board’s expectations into a clear plan with milestones, owners and evidence you can point to if anyone asks what your trustees did to protect your members.
FAQs: trustee accountability in the digital age
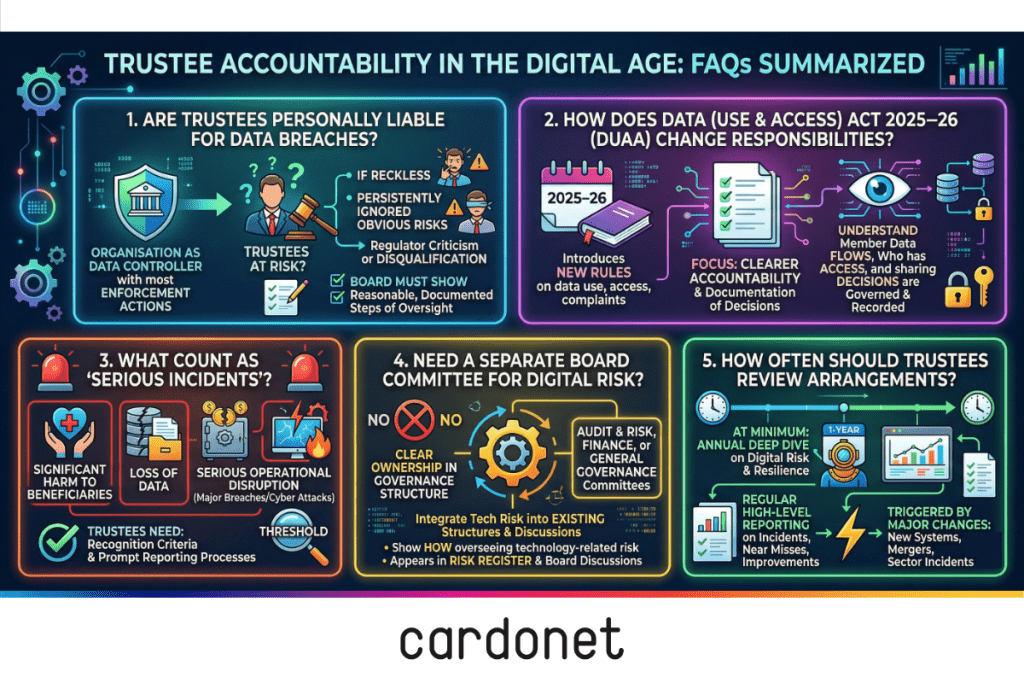
1. Are trustees personally liable for data breaches at a membership body?
In most cases, enforcement action is taken against the organisation as data controller, but trustees can be criticised or, in extreme cases, disqualified if they have been reckless or have persistently ignored obvious risks. Regulators focus on whether the board took reasonable, documented steps to oversee data protection and cybersecurity, in line with the ICO’s accountability and governance expectations.
2. How does the Data (Use & Access) Act 2025–26 change our responsibilities?
The Data (Use & Access) Act 2025–26 introduces new rules around data use, access and complaint handling, with an emphasis on clearer accountability and documentation of decisions about personal data. For trustees, this reinforces the need to understand where member data flows, who has access, and how decisions about data sharing are governed and recorded, as highlighted in MemberWise’s DUAA explainer for membership organisations.
3. What counts as a “serious incident” we must report to the Charity Commission or regulator?
Guidance points to incidents that result in, or risk, significant harm to beneficiaries, loss of data, loss of funds, or serious operational disruption, including major data breaches or cyber attacks. Trustees should ensure they have criteria and processes in place to recognise when an incident crosses that threshold and to report promptly, drawing on plain English summaries such as HCR Law’s article on Charity Commission serious incident reporting updates.
4. Do we need a separate board committee for digital risk?
Not necessarily. What matters is that digital risk, including data protection, cybersecurity and business continuity, has clear ownership in your governance structure and appears in your risk register and board discussions. Some membership bodies allocate this to audit and risk, others to a broader governance or finance and risk committee, but in all cases trustees should be able to show how they oversee technology related risk.
5. How often should trustees review cybersecurity and continuity arrangements?
At minimum, boards should receive an annual deep dive on digital risk and resilience, alongside regular high level reporting on incidents, near misses and progress against improvement plans. Reviews should also be triggered by major changes such as new systems, mergers, or significant incidents in your organisation or sector, and can be informed by checklists like the 2025 annual data protection checklist.



You must be logged in to post a comment.