
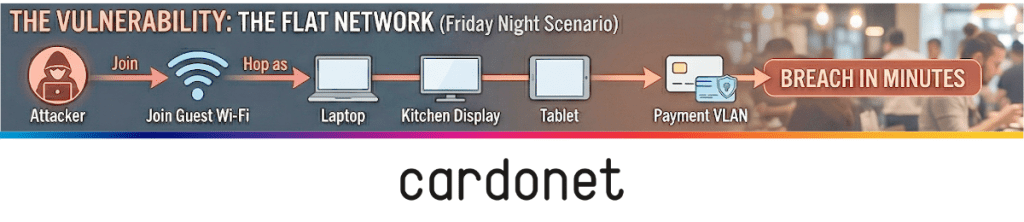
It’s 7:30pm on a Friday. The dining room is full, your POS terminals are taking payment from card after card. But somewhere on your network, an attacker who joined your guest Wi‑Fi an hour ago is quietly harvesting customer and payment data.
In almost every breach we see, the root cause is the same: a flat network where guest Wi‑Fi, staff devices and payment systems all share the same infrastructure.
In 2023, a ransomware attack on Yum! Brands – parent of KFC and Pizza Hut – forced the temporary closure of hundreds of UK restaurants while systems were recovered.
The attackers didn’t need exotic tools. They needed a foothold and a network that let them move freely once they were in.
Why restaurants are such easy targets for cyber security breaches
Restaurants process large volumes of card payments, stay open long hours, and often rely on lean IT support. High transaction volume, complex estates and limited specialist resources make them attractive targets for attackers who specialise in payment data.
The UK Government’s Cyber Security Breaches Survey 2025 reports that 43% of UK businesses experienced a cyber security breach or attack in the previous 12 months, which equates to roughly 612,000 organisations. That’s the backdrop your restaurant operates in.
In a typical site, POS terminals, back‑office systems, staff laptops, Wi‑Fi access points, kitchen screens and delivery tablets are plugged into the same logical network. If an attacker compromises any one of those through a phishing email to a manager, a weak remote access tool or a rogue device on guest Wi‑Fi, they can start probing sideways until they find something more valuable.
If there is no segmentation, nothing stops that lateral movement.
The hidden cyber security flaw in most restaurant networks
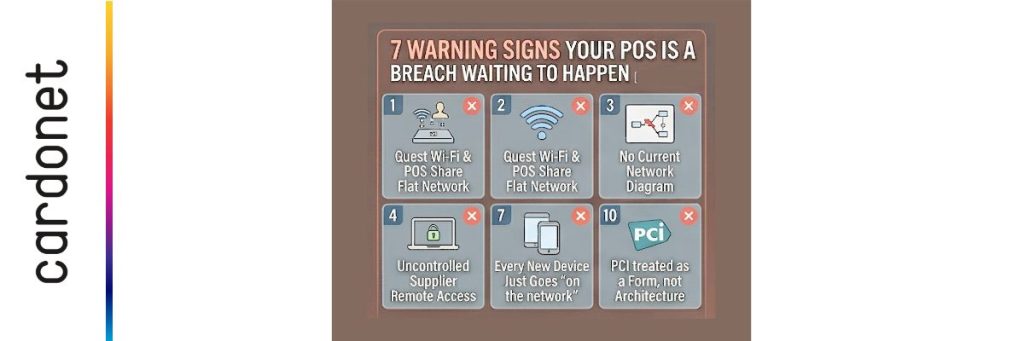
The single most common weakness we see in restaurant environments is not no MFA or out‑of‑date antivirus. It is a flat network where everything is on one segment and is able to talk to everything else.
Picture a three‑site group. Guest Wi‑Fi is broadcast from the same access points that serve your POS terminals. There is no separation between front‑of‑house devices, payment systems and back‑office servers. A guest, or an attacker posing as one, joins the Wi‑Fi and starts scanning: the POS terminals appear, then the back‑office server responds and from there, it’s a question of time and technique, not whether the environment is reachable.
The restaurants I worry about most are the ones that have modernised aggressively with online ordering tablets, QR code menus, loyalty apps and multiple delivery aggregators all going onto the same flat network they’ve always had. Every innovation quietly widens the blast radius of a single breach unless the underlying network design changes with it.
The National Cyber Security Centre’s network security guidance has been clear for years: network separation and segmentation are core to limiting the impact of compromise and restricting lateral movement.
The principle is simple – if one part of your environment is breached, it should not automatically give an attacker a route to everything else. In a restaurant, that means a mistake on guest Wi‑Fi should never be able to reach cardholder data.
What PCI DSS v4.0 really means in practice for your restaurant
PCI DSS v4.0 is now the live global standard for card payment security. It replaced v3.2.1 for assessments from 31 March 2024.
If you accept card payments in your restaurant, you are in scope – whether you run one site or twenty.
Three shifts matter most:
- Encryption. Higher expectations for how cardholder data is encrypted and protected at rest and in transit.
- Monitoring. Stronger requirements for logging, monitoring and acting quickly when security controls fail.
- Shared responsibility. Clearer rules on how responsibilities are divided between merchants and service providers such as POS vendors and payment gateways.
A good high‑level overview is UpGuard’s PCI DSS 4.0 compliance guide which underlines that these obligations apply to any business handling cardholder data, including hospitality.
Outsourcing payment processing does not shift accountability. Your provider may secure their platform, but you are still responsible for your own environment, including network design, access control, endpoint security and how your systems connect into the payment flow.
In blunt terms: a “good enough” flat network that was never designed with segmentation in mind is going to struggle under v4.0, even if your POS software is technically compliant.
How to redesign your restaurant network without ripping everything out
You don’t need a full rebuild to fix this. You do need to be intentional. For most restaurant estates, the work falls into three steps.
1. Map what’s really there
Draw your network as it exists today. List every device that touches your payment environment: POS terminals, back‑office servers, handheld ordering devices, Wi‑Fi access points, kitchen screens, delivery and ordering tablets, remote access tools.
Then ask – and write down the answers:
- Which of these devices are on the same logical network as guest Wi‑Fi?
- Which can talk to your POS terminals without going through a firewall?
If the honest answer is “we don’t know”, assume the worst until you can prove otherwise.
2. Isolate the payment environment
Create a dedicated network segment (VLAN) for payment systems – your cardholder data environment. Only devices that genuinely need to communicate with the POS infrastructure should be able to see it. Guest Wi‑Fi gets its own VLAN, with no route into internal systems, while staff laptops and office systems go onto a different one and kitchen displays and other operational technology sit on yet another.
Firewalls control traffic between segments with explicit rules. Anything not explicitly allowed is blocked and logged. A device on guest Wi‑Fi should not be able to see a POS terminal at all.
3. Watch what happens – and act
Segmentation without visibility is only half a solution. You need monitoring that alerts you when something odd happens. If a device on guest Wi‑Fi is trying to reach the cardholder data environment, or a POS terminal is making outbound connections to an unfamiliar address, you need to know.
For multi‑site groups, centralised monitoring matters. Without it, each restaurant becomes a separate blind spot. With it, you can spot patterns – the same suspicious traffic appearing at several sites, for example – and respond before a local incident becomes a group‑wide problem.
When you compare this effort against the cost of a serious breach – direct financial loss, incident response, potential regulatory action, lost covers and damaged reputation – the economics are not close. The government’s 2025 survey gives examples of disruptive breaches costing thousands of pounds even before reputational impact is fully factored in.
What a secure restaurant network looks like in one glance
In a well‑designed restaurant network:
- Guest Wi‑Fi only reaches the internet – not POS, not back‑office systems.
- POS terminals and payment servers sit on their own segment, with tightly controlled access.
- Staff laptops, office systems and management tools sit on a different segment, with no direct route into the payment environment.
- Kitchen screens and other operational tech are isolated from payment systems.
- All inter‑segment traffic passes through a firewall with clear, logged rules.
- Monitoring runs across the whole estate, including evenings and weekends.
You don’t need the fanciest kit to achieve this. You need clear boundaries and the confidence that if something goes wrong in one corner of the network, it doesn’t automatically put every card you process at risk.

Three moves you can make immediately
You don’t have to fix everything right now. Start here.
- Send one hard email.
To your IT partner or internal team:
“Please send a current diagram showing every VLAN in our restaurants, which devices sit in each, and exactly how – if at all – guest Wi‑Fi can reach our POS terminals.”
Their reaction will tell you a lot.
- Ask how PCI DSS v4.0 is actually being met.
Not “are we compliant?” – but: how is card data encrypted, how are logs reviewed, and who is responsible for what between you and each provider?
- Get one external view.
A short, focused audit from someone who understands both restaurants and security will surface issues that internal teams have normalised. That’s the starting point for Cardonet’s own work with hospitality operators.
If you want that external view, Cardonet’s restaurant cyber security explains how we assess your real network and POS estate – not a generic checklist – and will show you exactly where segmentation, monitoring and PCI DSS v4.0 expectations currently don’t line up.
FAQs: restaurant POS security
1. Does offering guest Wi‑Fi automatically put my POS system at risk?
Not by itself. The risk comes when guest Wi‑Fi and payment systems share the same network segment or can reach each other without going through a firewall. Proper segmentation keeps guest traffic away from your cardholder data environment, which is exactly what the NCSC’s network design principles are designed to achieve.
2. What has PCI DSS v4.0 changed that actually affects restaurants?
For most operators, the big shifts are higher expectations around encryption, more emphasis on continuous monitoring and log review, and clearer responsibility splits between you and your providers.
3. My POS provider says they are PCI compliant. Isn’t that enough?
No. Their compliance covers their platform. You are still responsible for your own network, devices and processes, and for how they connect into that platform. Shared‑responsibility guidance from PCI specialists makes that explicit.
4. How often should we review our restaurant’s cyber security?
At least annually, and after any significant change: new POS platform, new site, major refit, new delivery integration or a change in how remote access works. With v4.0’s emphasis on ongoing monitoring, once a year and forget about it is not realistic anymore.
5. Is this level of security only realistic for big chains?
No. Segmentation, basic monitoring and clearer responsibility splits are all achievable for independent operators too. The reporting mechanics scale with transaction volume, but the core design principles are the same whether you run a single site or a national group.



You must be logged in to post a comment.