
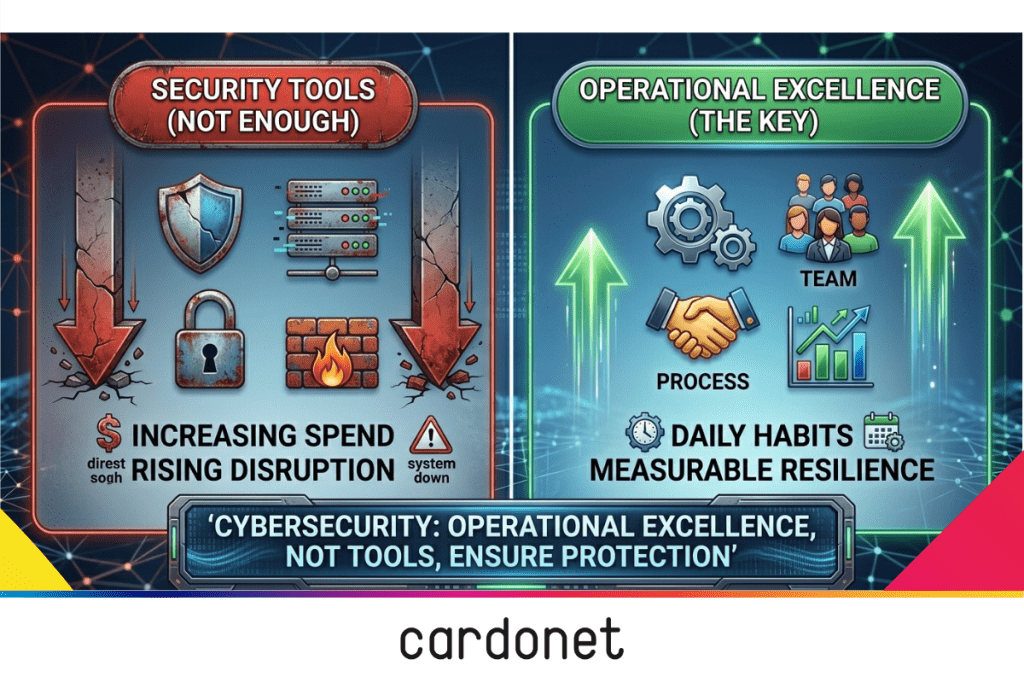
If security were simply about fancy tools, UK organisations would be immune to high levels of disruption from relatively routine cyber incidents. Spending on security technology is on the rise but so (as the UK government’s latest Cyber Security Breaches Survey makes clear) is cybercrime. Data shows that just over four in ten UK businesses – and a substantially higher share of medium and large firms – experienced a cyber breach or attack in the last year despite widespread investment in controls. The key differentiator is how the organisation runs around the tools, not the tools themselves.
Imagine doing the “right thing” and rolling out organization-wide endpoint protection, multi‑factor authentication, cloud backups, and alerts set up to monitor attempts. When an admin account is compromised, key systems can be encrypted within hours, stalling operations and wasting time and money.
No tools can counteract the impact of a weak operating model around change, access, recovery, and decision‑making under pressure.
Guidance from the National Cyber Security Centre (NCSC), such as its Cyber Assessment Framework, highlights this. NCSC’s guidance on preparing for severe threats emphasises maintaining operations and rebuilding IT at pace – an operational discipline as much as a security one – in documents like its guide on how to prepare for and plan your organisation’s response to severe cyber threats. When you read these alongside the UK government’s proposed Cyber Governance Code of Practice, a pattern emerges: operational excellence now sits at the heart of cyber resilience.
Why cyber risk is really an operations problem
Look again at the fictional organisation that “did everything right” from a tooling perspective but still ended up being crippled. Looked at it through an operations lens, a different diagnosis can emerge. Perhaps there was no rehearsed incident response plan, maybe change freezes were informal and inconsistently followed or vendor access could have been granted quickly and revoked slowly, if at all.
The security stack was working as designed – the way the organisation operated around it was not.
The Cyber Security Breaches Survey highlights that cyber incidents often result in tangible operational disruption – loss of network access, systems being taken offline, and dependency on third‑party services that themselves have been compromised. Those are not “IT problems”; they are business continuity failures that are felt across logistics, customer service, finance, and supply chains.
When nationally significant cyber attacks are being recorded on a regular basis, you can no longer ask whether you can prevent every breach but whether or not your organisation can continue to operate when one lands.
How weak operational discipline destroy cyber security
When a breach investigation finishes, public statements often talk about “sophisticated attackers” and “unprecedented threats”. The internal post‑mortem, if honest, usually tells a much more mundane story:
- An unrevoked account from a departed employee.
- A supplier with broader access than anyone realised.
- A critical patch delayed because of worries about short‑term disruption.
None of those are zero‑day exploits, they are operational gaps.
Weak operations create blind spots where no one is clearly accountable for data flows, privileged access, or third‑party dependencies. They reward speed over discipline, making exceptions the norm and “temporary” workarounds immortal. And they prevent learning – the same issues recur because there is no structured way for incidents, near misses, and audit findings to change how the organisation actually operates.
Survey data backs this up. Too many organisations still lack formal incident response processes, do not exercise their plans regularly, and treat supplier governance as a contractual add‑on rather than an operational discipline. Cardonet’s own guidance on IT security services and IT audits emphasises that structured assessment, monitoring, and process improvement need to sit alongside tools if you want risk to fall in a measurable way.
In other words, “more security budget” is an incomplete answer; without operational excellence, you are pouring money into a leaky process.
What operational excellence in cybersecurity looks like
Operational excellence in cybersecurity is about how your organisation behaves on a daily basis.
At a practical level, organisations that treat cyber security as a product of operations share a set of characteristics. They:
- Have documented incident response plans tied directly to their essential business functions, and those plans are regularly exercised, as per NCSC’s guidance on response and recovery planning.
- Understand which systems and processes are truly mission‑critical and have engineered “safe degradation” paths so they can run in a reduced but controlled mode during an incident.
- Manage supplier relationships on the assumption that third‑party failure is inevitable and design both contracts and technical integration accordingly.
Seen through that lens, cyber security stops being a defensive tax on innovation and becomes a performance discipline. Habits that reduce cyber risk (ownership, processes, responses, and learning) also cut operational waste, downtime, and rework.
If you drive operational excellence you will find your cyber security metrics improve as a side effect because they are simply another way of measuring how well you run the business.
Building a cyber security‑first operating model step by step
If you accept that cyber security outcomes are shaped by operations, the natural question is what to change first. For most organisations, the answer is not a wholesale redesign of their operating model but a sequence of deliberate, executable steps that bring cyber security and operations closer together.
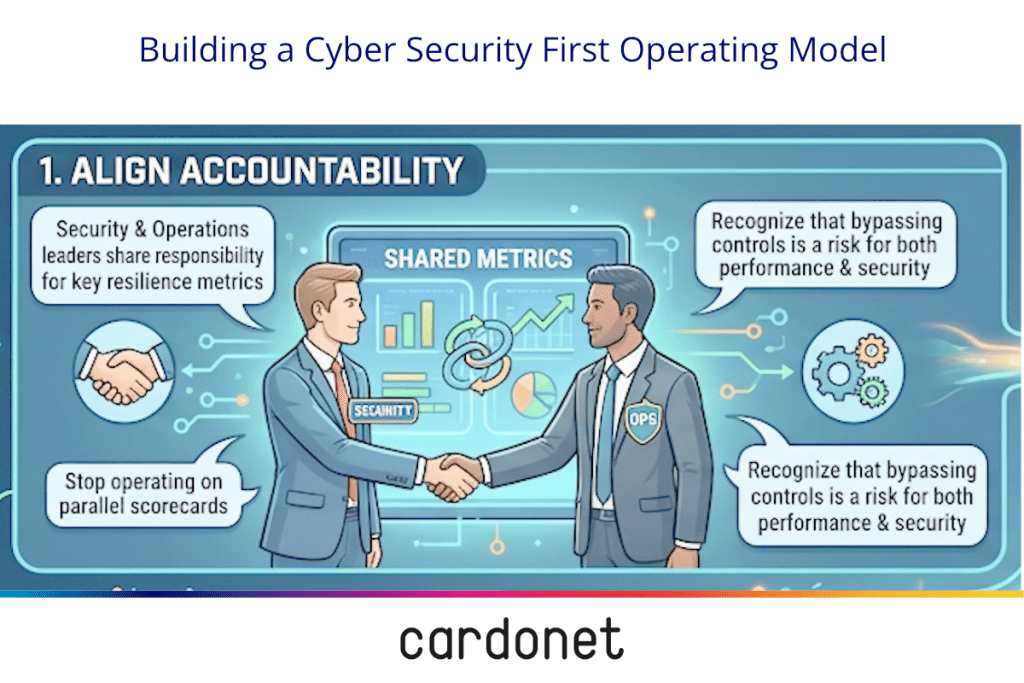
- Align accountability. Cyber security and operations leaders should share responsibility for key resilience metrics rather than operating on parallel scorecards. Decisions to bypass a control for short‑term convenience must be recognised as a risk to both cyber security and operational performance.
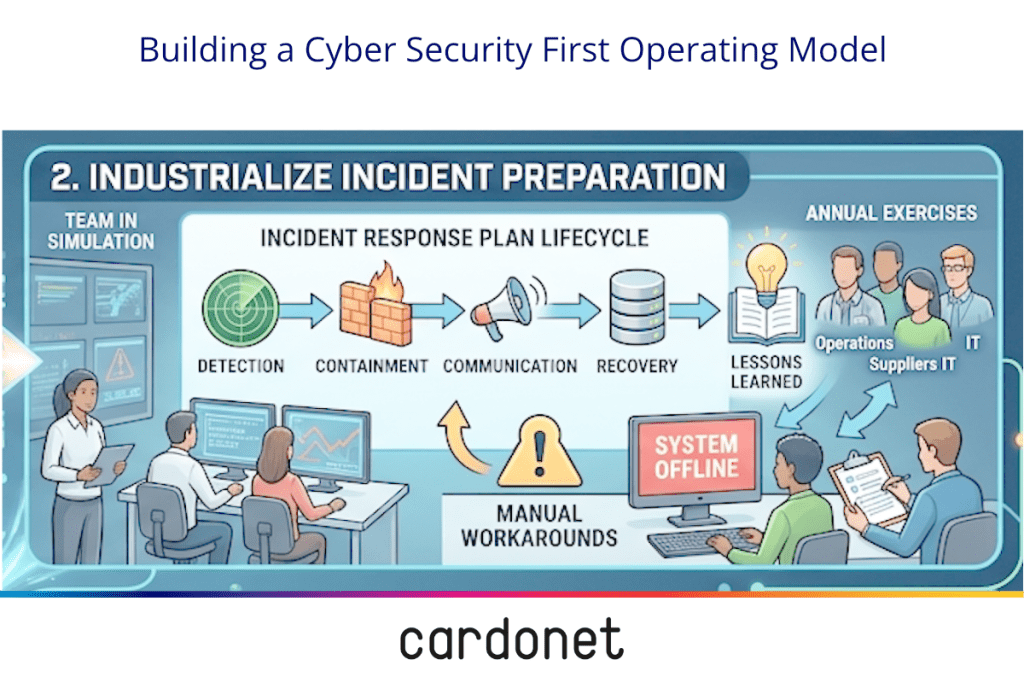
2. Industrialise incident preparation. Use widely available guidance to build or refine a documented incident response plan that covers the full lifecycle (detection, containment, communication, recovery, and lessons learned) and then schedule realistic exercises, at least annually, which involve operations, communications, and supplier management teams, not just IT. These should be designed to stress manual workarounds and offline plans for when core systems are unavailable.
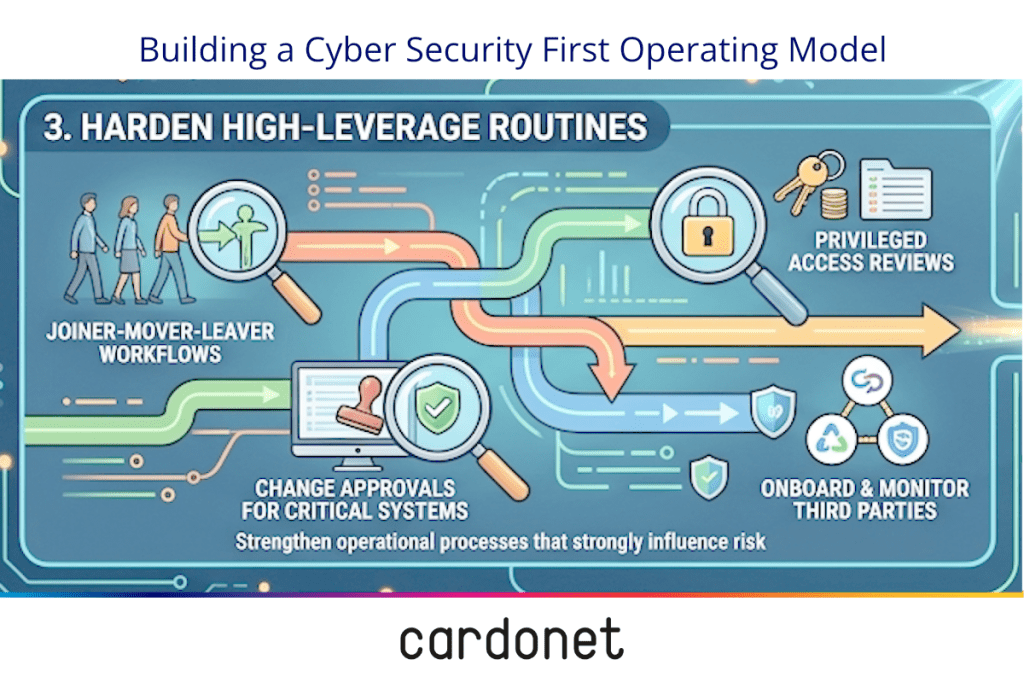
3. Harden the high‑leverage routines. Focus on the operational processes that most strongly influence risk: joiner‑mover‑leaver workflows, privileged access reviews, change approvals for critical systems, and the way you onboard and monitor third parties.
4. Embed learning into operations, not just cyber security. After incidents and major near misses, run reviews that explicitly examine both technical and operational contributors – how decisions were made, how information flowed, where processes broke down – and then change how the organisation actually works. The NCSC’s frameworks place as much emphasis on lessons learned as on initial response. Over time, this turns security from a project into a culture.
How to measure cyber security as an operational outcome
If cyber security is a product of operational excellence, you need a scoreboard that reflects that reality. Traditional metrics like the number of blocked attacks or vulnerability counts have their place, but they do not tell you how well your organisation will survive the incident that gets through.
Boards and leadership teams need a set of indicators that connect cyber resilience directly to operational performance.
Some of these measures are straightforward.
- How long does it take you to detect and contain an incident, and how does that compare between exercises and real events.
- How often do you rehearse your incident plans with the people who will actually be in the room on the day.
- What proportion of high‑risk audit findings are closed on time, and how many trigger changes to operational procedures, not just technical configurations.
These are operational metrics wearing a cyber security badge.
Others are explicitly business‑focused. The breaches survey notes that incidents frequently result in network downtime, compromised websites, and loss of access to third‑party services, all of which can be expressed as lost revenue, delayed deliveries, or reputational harm.
Tracking the frequency, duration, and business impact of these disruptions over time, and tying improvements back to specific changes in operational practice, gives leaders a concrete way to see whether investment in operational excellence is paying off in resilience.
From a services perspective, this is also where a partner like Cardonet can help you join the dots. By combining security assessments, managed monitoring, and IT strategy advice into a coherent view of how technology, process, and operations interact in your business.
Why this matters for your business
Treating cyber security as an operational outcome changes how you allocate energy, not just money.
It moves difficult conversations out of the budget cycle and into the routines that shape culture and aligns you with where UK policy is heading.
From the Cyber Governance Code of Practice to NCSC guidance on severe threats, the thread is consistent: regulators and policymakers expect cyber to be embedded into business continuity, supply‑chain management, and everyday decision‑making.
Organisations that can demonstrate that integration, with evidence of rehearsed plans, clear ownership, and measurable improvements, will find it easier to build trust with customers, partners, and insurers.
From where I sit, the most resilient organisations in the next few years will not necessarily be the ones with the most advanced tools. They will be the ones that have done the hard operational work, aligning leadership, rehearsing response, hardening key processes, and learning fast when things go wrong.
Next steps: Protecting your business
If this has landed a little too close to home, resist the urge to buy another product first. Start by mapping one recent incident, near miss, or audit finding all the way back to the operational routines that made it possible, then change those routines and test them.
A practical way to accelerate that work is to bring cyber security and operations leaders into the same room for a structured review.
Ask Cardonet to run a joint security and operations review that maps your incident response, change management, and vendor processes against current UK cyber guidance. You will come away with a focused plan for strengthening resilience where it matters most.



You must be logged in to post a comment.